What CISA KEV Is and Isn’t – and a Tool to Help Guide Security Teams
Fri Feb 06 2026
Patch Management
Vulnerability
thecyberexpress.com
A new paper gives an insider’s perspective into CISA’s Known Exploited Vulnerability catalog – and also offers a free tool to help security teams use the CISA KEV catalog more effectively.
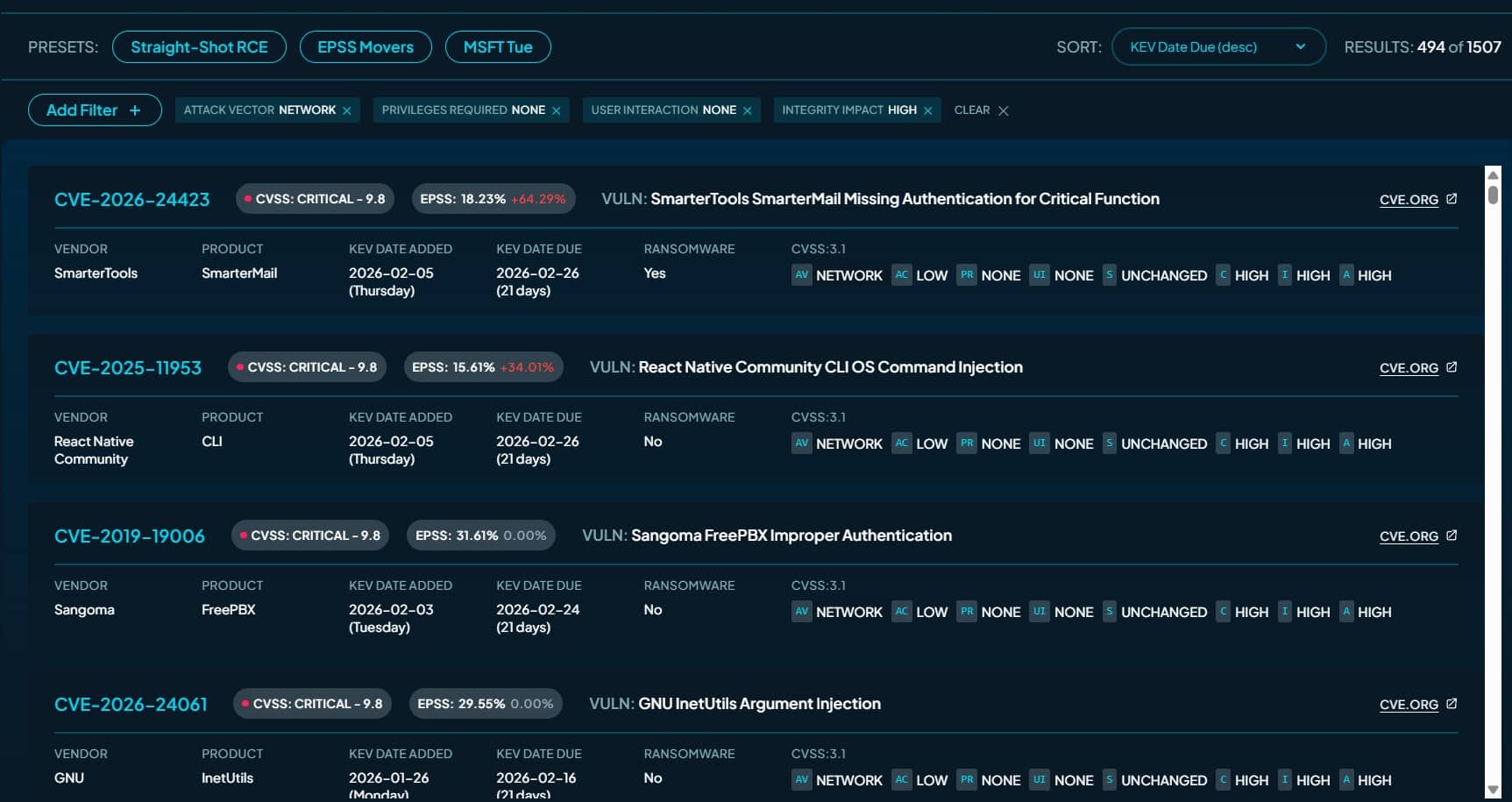
The paper, by former CISA KEV Section Chief and current runZero VP of Security Research Tod Beardsley, applies commonly used enrichment signals like CVSS, EPSS and SSVC, public exploit tooling from Metasploit and Nuclei, MITRE ATT&CK mappings, and “time-sequenced relationships” to help security teams prioritize vulnerabilities based on urgency.
The paper’s findings led to the development of KEV Collider, a web application and dataset “that encourages readers to explore, recombine, and validate KEV en...