Why Simple Breach Monitoring is No Longer Enough
Mon Apr 06 2026
IAM
Malware
www.bleepingcomputer.com
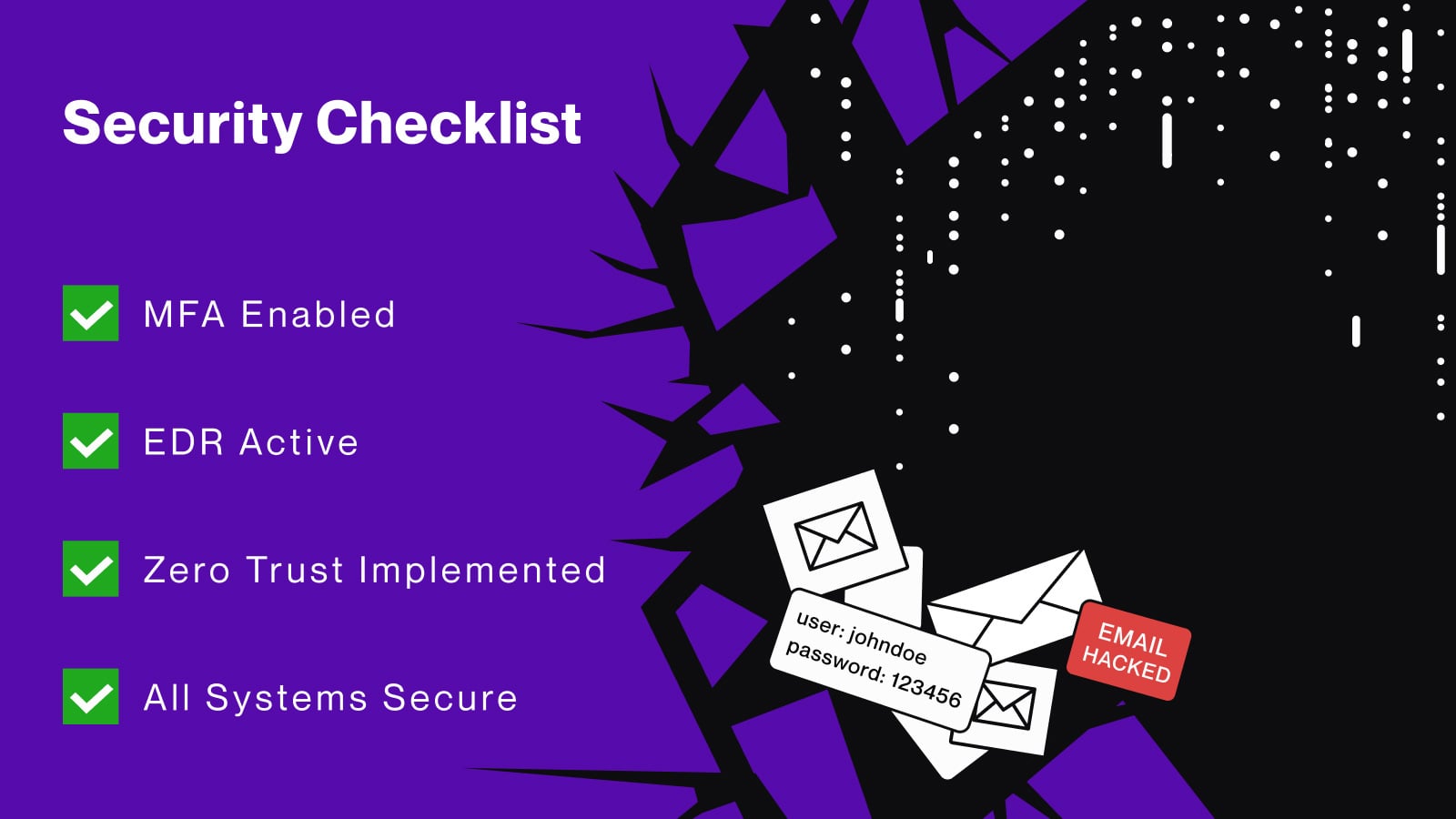
Infostealers are harvesting credentials and session cookies at scale, bypassing traditional defenses. Lunar explains why simple breach monitoring alone can't keep up with modern credential-based attacks. [...]